While delivering on the promise of streamlined efficiencies and operational insights, smart IoT devices also present a new and more widespread threat to users and personal data.
No one really needs reminding of the security implications of IoT. Think of the damages a hacker could achieve through compromising a connected home security system, a vehicle, a copier connected to your corporate network, or even a medical device. The stakes are high and protecting an always-on IoT network is essential. Surprisingly few IoT devices have been designed with security as a paramount consideration. This leaves users vulnerable because IoT devices can act as a “back door” to the network that hosts them, enabling a multitude of attacks, device zombification, and botnets.
IoT security starts with Machine Identities. Security, trust, consent, and identity management are the cornerstones of IoT success: it’s not about the devices, but about the trusted and authenticated services they offer.
Safe IoT deployments require not only trusting the devices to be authentic and to be who they say they are but also trusting that the data they collect is real and not altered. If one cannot trust the IoT devices and the data, there is no point in collecting, running analytics, and executing decisions based on the information collected.
Protecting Machine Identities is as important as protecting human identities. Ninety-six percent of companies agree that effective protection of machine and human identities is critical to the long-term security and viability of their companies, but 80% struggle with the delivery of important machine identity protection capabilities. 90% of companies believe machine identity protection will be equal or higher in priority than human identity protections.
Machine identities can be protected with device X.509 digital certificates. Certificates are used in place of passwords to authenticate trusted connections between network endpoints. Put simply, a certificate is an assurance of identity and authorization using a secret private key validated with a known public key. Unlike passwords or other methods based on shared secrets, certificates can’t be stolen en route or otherwise maliciously appropriated by an impostor since, with client-certificate authentication, the private key never leaves the client and isn’t sent to the server. Proper hardware measures must be in place to secure the private key is stored in a secured partition. Firmware and secure storage partitions are to be de-coupled, thus allowing for separation of firmware and certificates provisioning.
Certificate-based mutual TLS (mTLS) authentication refers to two parties authenticating each other through verifying the provided digital certificate so that both parties are assured of the others’ identity.
Implementing mTLS for the IoT requires setting up a proper public key infrastructure. IoT public key infrastructure (IoT PKI) is a set of tools, policies, and procedures needed to provision, manage, distribute, use, store & revoke digital client certificates and manage public-key encryption specific to resource-constrained IoT devices.
The aim of PKI is to provide confidentiality, integrity, access control and authentication.
While PKI ensures access control to the IoT server infrastructure, access policies are needed to further refine resource access. An access control solution built on context-based security policies considers the particular set of circumstances when the request to access data is made – the resource, the environment, the requester. A great example of access policies is Amazon’s AWS IoT policies, part of their IAM – Identity and Access Management system. An AWS IoT policy is a JSON document that contains one or more policy statements. Each statement contains an Effect, an Action, and a Resource. The Effect specifies whether the action is allowed or denied. The Action specifies the action the policy is allowing or denying. The Resource specifies the resource or resources on which the action is allowed or denied.
Implementation of the above-listed measures ensures enterprise-level security for IoT solutions.
Resources:
- PKI: The Security Solution for the Internet of Things
- The Identity of Things is here
- IoT identity, device management
- What is IoT PKI?
- Securing The Enterprise With Machine Identity Protection
- How to manage IIoT authentication and protect machine identities
- An Introduction to Mutual SSL Authentication
- Implementing IAM Policy for IoT Devices
- AWS IoT Policies
Hello Martin
I am Hugues Mialhe, from France
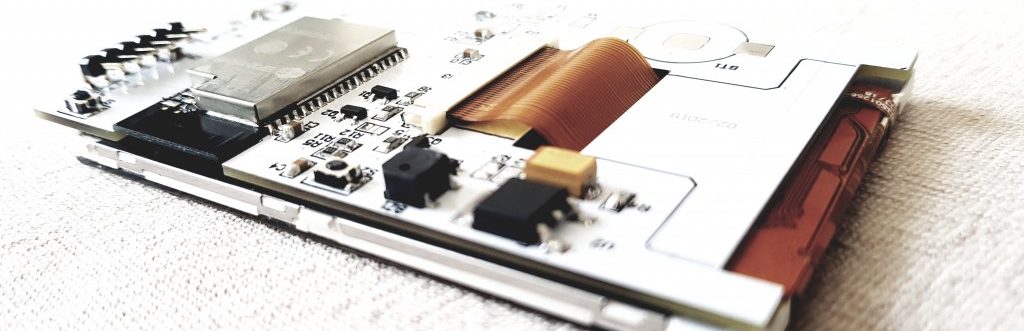
I bought you a daikin online controler few years ago.
THis year, I can’t make it work because I guess of the ntp which doesn’t give the right schedule.
Coud you help me please !
I can’t find your emails, maybe that was with a previous mailbox that we shared.
Down is my new one !
Big need of help !
Ohoh, I might have found the solution !!!
Disconnecting and reconnecting the card seems to have the new stp server link enabled 🙂
Sorry for this dummy question !!!
Don=’t hesitate to send me your contact as I lost your email.
Thank you again for your kindness and intelligence Martin, you helped me a lot with your work !
Best regards
Hugues
Oups again
I might definitely need your help :
The clock is ok when I plug the usb, but seems not to go forward : stay at the same time !
Heeeelp !
Hello,
Have you changed your internet service provider recently? Many ISPs now block NTP requests, therefore the embedded devices fail to fetch correct time. Unfortunately, there is no cure for that, unless maybe running your own NTP server on a Raspberry Pi for example.