Connected devices and sensors are the fastest growing sources of data. Billions of records are being generated daily around the globe and data transported across networks to be consumed where needed. Security of data in transit or at still in that context (especially when it comes to sensitive personal data) is quite important.
Back in 2011 Fitbit portal exposed on the Internet thousands of records of intimate activities of their subscribers. How did that affect the company’s reputation and customer trust? Damage is done to the whole IoT industry, not just the company that allowed that to happen.
As customers we want our data encrypted during transport, stored safely and kept private. The collation of multiple points of data can quickly become personal information as events are reviewed in the context of location, time, recurrence, etc. The regular purchase of different food types, for example, may reveal religion or ongoing health concerns. Health records, location details, energy use patterns and so forth private data can easily be used to reconstruct in great detail one’s life. This data is therefore naturally of interest to many. Governments, insurance companies, marketing/advertising agencies and certainly criminals are after it.
Unauthorized access to data isn’t the only problem. Connected devices are designed to be remotely controllable. With surprisingly many consumers relying on default product security credentials, it is strikingly easy to gain control of connected appliances. Dynamic DNS services are a honeypot to those hunting for connected devices. One could easily end up with a spying thermostat or a fridge that sends spam or someone remotely controlling your smart home.
What makes it so hard to get security right? Design flaws, implementation flaws and mismanagement are often the source of vulnerabilities. Systems are “adequately secure” only relative to a perceived threat. Absence of obvious insecurities is not a good indication that a system is adequately secure. Users also have a good share in decreased security by not updating firmware, using poor passwords, inadequate fire-walling. “Security” through obscurity is very common and seems that folks still believe in it.
Overall security concerns are at the top of the list of barriers to the IoT adoption, with consumers awareness in this area on the rise. Any IoT business model must adequately address these concerns in order to be successful and sustainable.
100% ACK.
But – didn’t you write about moving your computing stuff into the cloud? That doesn’t really fit for me, sending my (private) data to a cloud computer which I don’t control…
Do you have any ideas for the solution of the problems you mentioned?!
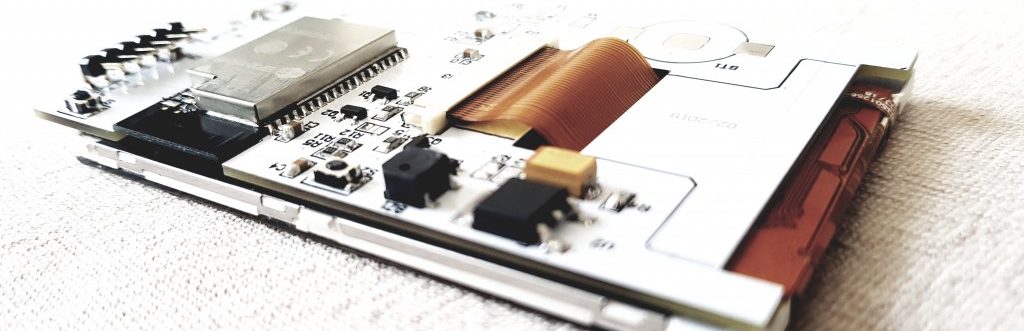
You assume that keeping your private data locally guarantees you security, that may give you false sense of security. There are couple aspects here – data in transit and data at still. I address the data in transit issue by transmitting it over SSL for HTTP traffic. My RFM12b traffic is unencrypted and anyone within 50m of my house may intercept and view it freely; I believe this is highly unlikely for the place I live, but for dense urban areas that may not be the case. Jeelib doees support basic encryption, see http://jeelabs.org/2010/02/23/secure-transmissions/ . Data at rest (or stored data) is a different story. I do keep my data unencrypted on the cloud now, so potential hack on my cloud storage will result in the data leaking. Simple encryption and the sending end will help increase security in case of data leak, but will also add to the complexity of running reporting on top of the data. Of course asymmetric encryption would be preferable, but that adds significant overhead. I have done such projects at work (enterprise level) for sensitive (HR) data. There is a balance for home automation projects that I am yet to find 🙂
Cloud hosting services like Amazon’s AWS keep the storage services security patched for you so you don’t have to worry about that. Thinking about scale (adding more places to your home automation), you’ll end up transporting your data over the network at some point. I do believe cloud hosting is the way to go.
Pingback: Free signed SSL certificate for my blog | Martin's corner on the web